Last Updated on by Vairo Kremanis
User Behavior Analytics Solutions and arrangements that depend just on standards to recognize infringement and potential dangers experience the ill effects of excessively numerous false positives and the failure to distinguish beforehand obscure risk designs.
To address these weaknesses, security examination arrangements are beginning to join client behavioral investigation (UBA).
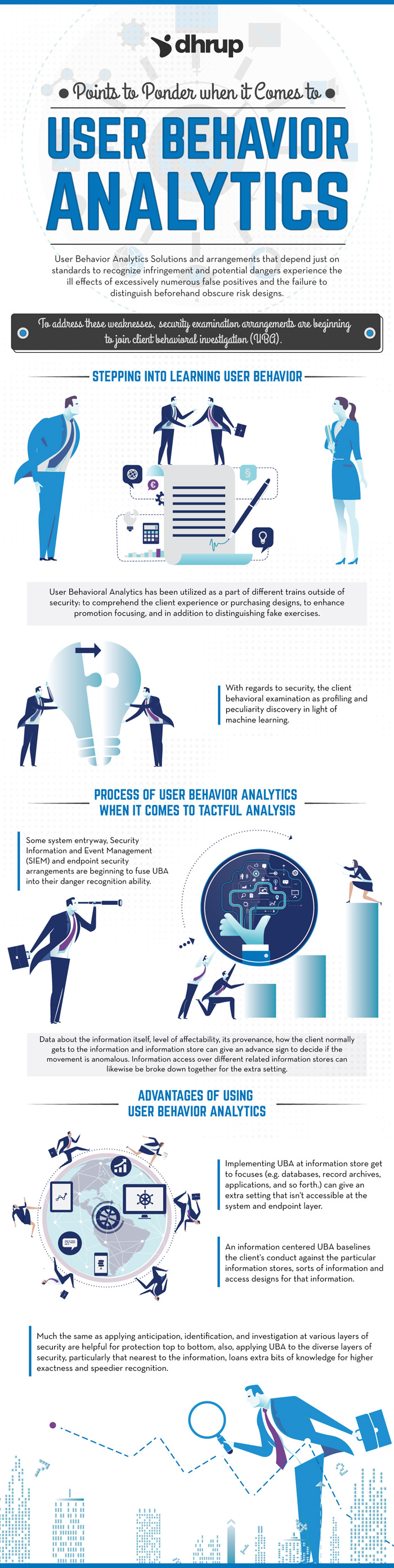
Stepping into learning User Behavior
User Behavioral Analytics has been utilized as a part of different trains outside of security: to comprehend the client experience or purchasing designs, to enhance promotion focusing, and in addition to distinguishing fake exercises. With regards to security, the client behavioral examination as profiling and peculiarity discovery in light of machine learning.
UBA profiles and baselines client exercises and their associates to survey what constitutes a person’s ordinary versus irregular conduct. Different substances besides clients may likewise be profiled, for example, gadgets, applications, and endpoints. The recognizing highlight of UBA is the utilization of machine learning and measurable models, past standards to distinguish unusual client practices that could be a risk. The utilization of machine learning empowers beforehand obscure examples to be recognized, the lessening of false positives activated from static decides that don’t adjust to every client or evolving practices, and the need to characterize rules for each potential infringement.
Process of User Behavior Analytics when it comes to tactful analysis
Some system entryway, Security Information and Event Management (SIEM) and endpoint security arrangements are beginning to fuse UBA into their danger recognition ability. The UBA fused into these arrangements, for the most part, concentrates on investigating occasions and logs from systems and endpoints. They recognize dangers from malware on endpoints and in addition assaults coming through system firewalls or exfiltration exercises uncovered through the filtering of system parcels.
While UBA connected to the system and endpoint layers are valuable to give barrier top to bottom, extra setting, for example, area and gadget from where information is gotten to, what information is gotten to in a similar session, volume, run of the mill get to design for comparative information and information stores, time and regularity of access, can be conveyed to hold up under while applying UBA around the information itself, particularly when the information is touchy.
Data about the information itself, level of affectability, its provenance, how the client normally gets to the information and information store can give an advance sign to decide if the movement is anomalous. Information access over different related information stores can likewise be broke down together for the extra setting.
Advantages of using User Behavior Analytics
Implementing UBA at information store get to focuses (e.g. databases, record archives, applications, and so forth.) can give an extra setting that isn’t accessible at the system and endpoint layer. On account of the extra set, you can better pattern an insider’s typical versus strange conduct, identifying malignant or maverick insiders and also exercises from stolen accreditations, which would not be clear from simply examining exercises on the system. The kind of assault from an advantaged client like Snowden must be recognized by applying UBA on the information and information stores he gets to.
An information centered UBA baselines the client’s conduct against the particular information stores, sorts of information and access designs for that information. Irregular practices around the qualities, volume, and blend of information or information stores a representative gets to will probably be distinguished from an information-centered UBA. The extra setting bolsters more prominent recognition exactness to operationalize all the more convenient insurance or remediation to potential dangers on delicate information.
Much the same as applying anticipation, identification, and investigation at various layers of security are helpful for protection top to bottom, also, applying UBA to the diverse layers of security, particularly that nearest to the information, loans extra bits of knowledge for higher exactness and speedier recognition. Therefore, search for client behavioral examination abilities in your information security arrangements too.








